
What’s the difference between a Console Port and a Management Port?
It’s a difference you need to know!!!

One of the questions that many of our customers and partners ask in relation to out-of-band management for their networking infrastructure is what the difference between the dedicated management port and the console port on some of their networking infrastructure equipment are? To answer that question lets go back to the basics of networking.
There are 3 planes defined in the networking infrastructure world: Data Plane, Control Plane, and Management Plane.
- Data Plane is where the use traffic flows and include forwarded frames and packets that contain user data.
- Control Plane is where the routing information and protocols that control the flow if the user data in the data plane reside.
- Management Plane is where the configuration traffic such as the commands to configure the switches and routers reside.
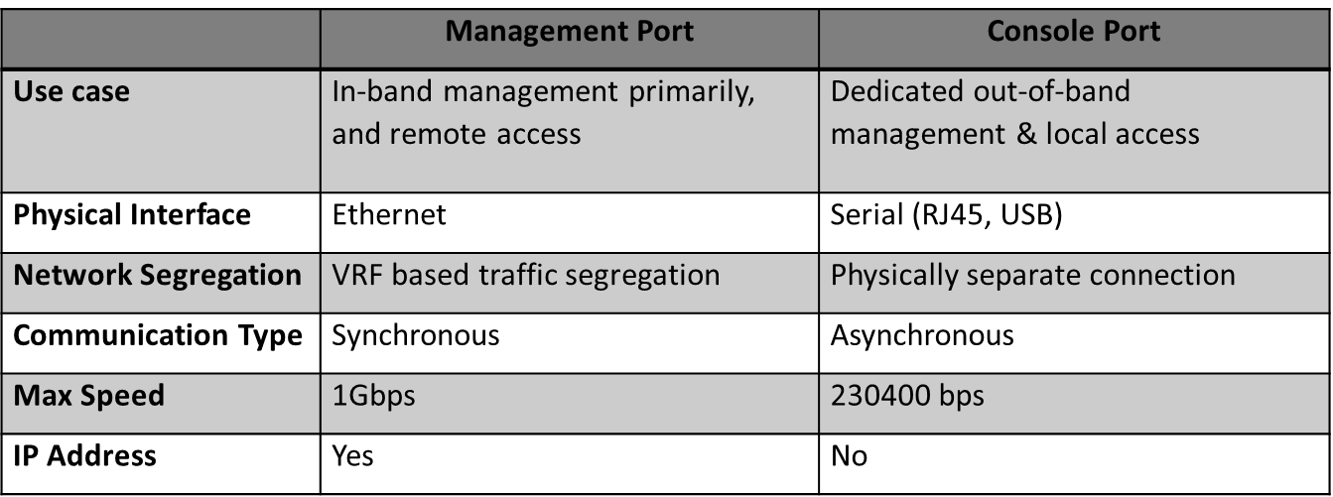
Now managing a network infrastructure can be done in two ways, one is known as in-band network management, where the in-band management traffic uses the same data plane as used by data traffic on the networking device. Another, more resilient way for managing networking devices, is using a dedicated out-of-band management network, where the management of network devices operate on a management plane that is separate from the data plane. And that is where the two different ports (management port, which is typically an Ethernet port and console port, which is always a serial port) come in.
OOBM is a more secure and resilient approach to managing a network infrastructure as it can function even during data traffic congestion, a device glitch or network attacks. A management port can be used for remote management and configuration of a networking device, where as the Console Port can be used, in conjunction with a console server, such as Lantronix SLC 8000, to implement a separate dedicated network to access the network devices in case the primary network goes down.
A user in this case can access the console ports of a Cisco switch, via a console server using a secondary network such as LTE or Wi-Fi and be able to remotely access the device to remediate issues or to quarantine devices affected by cyber-attacks. You can configure up to 15 simultaneous users to connect to a Console Port.
Some of the difference between the two ports are summarized in the table below:
It is important to note that the use of a dedicated out-of-band network using the console port is on the rise in the recent past due to increase in network attacks, and domestic and foreign cyber threats to critical network infrastructure. In fact the Cybersecurity and Infrastructure Security Agency (CISA), which is part of the Department of Homeland Security, and is the nation’s risk advisor, issued a security tip less than a year ago (ST18-001) recommending organizations, small and large, to implement dedicated out-of-band management solutions in order to substantially increase the resiliency of their networks.
CISA, recognizes that OoB management can be implemented physically, virtually, or through a hybrid of the two. Although additional physical network infrastructure additional infrastructure is required to implement and maintain a dedicated physical OoB management network, it is the most secure option for network managers to adopt.
Below are some additional recommendations on best practices for your network infrastructure security:
- Segregate standard network traffic from management traffic.
- Ensure that management traffic on devices comes only from OoB.
- Apply encryption to all management channels.
- Encrypt all remote access to infrastructure devices such as terminal or dial-in servers.
- Manage all administrative functions from a dedicated, fully patched host over a secure channel, preferably on OoB.
- Harden network management devices by testing patches, turning off unnecessary services on routers and switches, and enforcing strong password policies. Monitor the network and review logs. Implement access controls that only permit required administrative or management services (e.g., SNMP, Network Time Protocol, Secure Shell, FTP, Trivial File Transfer Protocol, RDP, SMB).











